Manage Login data in the most flexible way

We are pleased to be able to release privacyIDEA 3.9. This release is an example of how privacyIDEA is ment to centrally manage all you authentication in one place – since successful authentication is a matter of smooth workflows.
privacyIDEA aims to be a management system where the administrator can easily manage the authentication topic for the users. You as an administrator can manage the OTP tokens (TOTP, HOTP apps, Yubikeys), tokentype like SMS or Email, even FIDO2. All you need for two factor authentication.
And privacyIDEA is able to also verify the first factor. The static password.
Old authentication – new token types
But sometimes you might see, that two factor authentication does not work out as expected. That applications do not play well with FIDO2/WebAuthn. Yes, sometimes applications do not play well even with OTP tokens. Take an Email client, that caches the user password and sends it, every time it fetches the emails from the server. The request will fail if it is sent with the same OTP value a second time.
Successful Authentication is not always a matter of choose the most modern cryptographic algorithm or the latest authentication method.
Sometimes there is an old, nasty application that refuses to work well with the 2FA method you are enrolling in your company. But privacyIDEA wants to help you as administrator to manage all these challenges in one system.
With privacyIDEA 3.9 we introduce two new token types which might sound old and insecure, but which are supposed to enable you to take a step forward, even if some old applications want to hold you back.
The application specific password token is simply a static password that can be bound to a specific application. The old application will send an authentication request against privacyIDEA and privacyIDEA will realize, that this auth request originated from this application and allow such application specific password tokens enrolled for this application to be used for authentication. A user can have a specific password for e.g. his email client, save this in his smartphone and privacyIDEA will accept this only for login requests by this email client resp. mail server.
You may check the conceptual evolution of this feature on Github.
The day password token is a similar quirky thing. In certain situations having an OTP token that changes all 30 seconds or 60 seconds may be to changeable for some users or use cases. But using no second factor and relying on a never changing static password is also not an option.
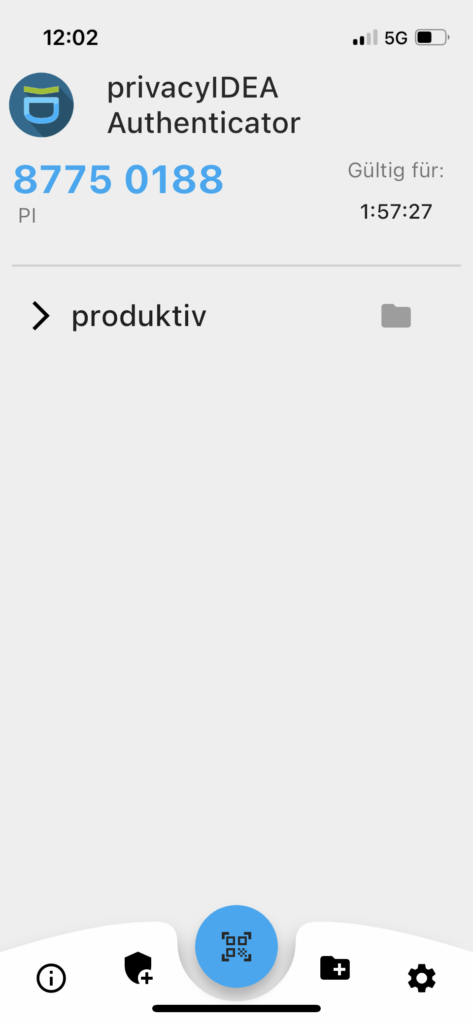
Why not have a token, that can be used for one hour? Or one day? The day password token in privacyIDEA 3.9 is a token type with a variable time window between one second and many days. During this time window the given code is valid during the whole time window and can be used as often as needed. It is similar to TOTP (in fact it is inherited from the TOTP token class), but has the above mentioned special effects.
This token type has its counter part in the privacyIDEA Authenticator App, which you can find in the Google Play Store and Apple App Store. The day password token is supported in the privacyIDEA Authenticator App starting with version 4.2.
Improving SSH Key Management
Managing SSH keys has been a bit cumbersome in the past. You as the administrator had to assign each SSH server to the SSH key, so that the user could use the SSH key to log to this server.
With privacyIDEA 3.9 you can now define service identifiers, which represent the servers. E.g. you could define an identifier “web servers” and assign SSH keys to this identifier.
Now you can simply have the SSH server identify as “web servers” to allow the login with this SSH key. This way it is easy as configuring the corresponding server, to add a new SSH server to the “web servers”.
The helper script privacyidea-authorizedkeys, which is supposed to run on the SSH servers has been modified so that it queires privacyIDEA for the corresponding service identifier.
Changelog
A new event handler can set the application assignment during enrollment. This helps with definding HOTP tokens as Offline-Tokens for the privacyIDEA Credential Provider. The PUSH token can do a decline, so that the authentication process is cancelled.
You can find the complete changelog at Github.
Install and Update
You can download and update privacyIDEA 3.9 via the community repositories for Ubuntu 20.04LTS and Ubuntu 22.04LTS or via the Python Package Index.
If you want to get involved, you can join the discussion at the Forum or coding at Github.





Start the discussion at community.privacyidea.org