We are pleased to announce the release of privacyIDEA 3.0.1 today. In this release, we did not implement any new features, but instead focused on stability. Our last major release privacyIDEA 3.0 came with several big changes. Most notably, it introduced a new PUSH token class. With this token class, […]
Whatsup
Proudly we talk about our release of the major version privacyIDEA 3.0, today. Changing the version number 2.23.5 to 3.0 indicates a lot of changes. Changes why you should take more care during the update process. And changes, why this article is a bit longer than usual. But relax! We […]
privacyIDEA will be at Chemnitzer Linuxtage 2019. See new features which will come in version 3.0
The new release 2.5 of the privacyIDEA ownCloud app allows the administrator to define which client should require 2FA and which is ok with only a password. This is based on the IP address of the clients. This way e.g. users would not need a second factor when accessing ownCloud […]
On Sunday February 3rd I will give a talk how you can use privacyIDEA to add enterprise grade multi factor authentication to ownCloud. privacyIDEA is easy. And flexible. It is probably the most flexible open source multi factor authentication systems around. And some scenarios are easy. So easy that you […]
privacyIDEA will be at the OpenRheinRuhr conference in Oberhausen, Germany. The conference is fixed stop in our yearly conference world tour, so we are looking forward to be in Oberhausen again, on November 3rd and 4th. Come and visit us at our stand an learn first hand about new cool […]
The Multi-Factor Authentication system privacyIDEA 2.23 comes with PRE event handling, recurring tasks, monitoring and statistics. The administrator thus has a lot of tools, to automate unforeseen scenarios and avoid manuel, tedious tasks and avoid errors.
The privacyIDEA project – the most flexible two factor authentication system – will have a booth at FrOSCon, the Free and Open Source Conference in Sankt Augustin, Germany on August 25th and 26th.
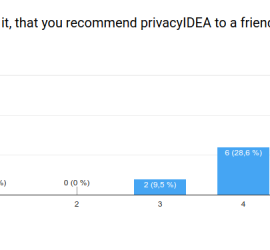
There were 21 users participating in the privacyIDEA user survey 1/2018. Thanks a lot for taking the time to answer all these questions! We will try to give an overview of the answers and we will even try harder to deduce some results and todos from these data. A former […]
End of April we will attend two conferences to present the interesting possibilities of privacyIDEA to the world. Grazer Linuxtage, Graz – Austria At the Grazer Linuxtage Friedrich will give a talk about how privacyIDEA can be an alternative for classical, proprietary two factor solutions like RSA SecurID, Vasco or […]