Please note: This howto is outdated. It refers to a rather old version of privacyIDEA. Please read the install documentation at readthedocs.
Starting with privacyIDEA 1.2 a debian package for Ubuntu 14.04 is availble.
Please note, that you will not be able to install it on 12.04, since there would be missing requirements. privacyIDEA depends on the following packages:
python-setuptools python-pylons python-qrcode python-netaddr python-ldap python-pyrad python-yaml python-configobj python-repoze.who python-httplib2 python-crypto python-docutils python-repoze.who-plugins
There are two PPA repositories available on launchpad: privacyidea/privacyidea-dev and privacyidea/privacyidea. The -dev repository is for development releases and testing. The privacyidea/privacyidea repo should contain stable releases.
Add the repository to your system and install privacyIDEA
To add the repository to your system run the following command:
add-apt-repository ppa:privacyidea/privacyidea
Fetch information on new content:
apt-get update
Install it:
apt-get install privacyidea
The package creates an SQLite database at /var/lib/privacyidea/token.sqlite. Of course you can use any other database backend. But using sqlite gets you up and running quickly.
Moreover the package contains a start-script /etc/init.d/privacyidea, that is running privacyidea in python-paster, a simple, lightweight webserver.
To start privacyidea run:
service privacyidea start
privacyIDEA is now listening on port 5001.
Create your admin account
Finally you need to create a first admin account to log in to the management interface:
privacyidea-create-pwidresolver-user -u admin -p test -i 1000 >> /etc/privacyidea/admin-users
Instead of using the weak password test, you should make up a cooler one.
Now you can login at https://yourserver:5001/ with the username “admin@admin” and the password you created.
Some performance data
The paster is a small webserver. The SQLite is not a state-of-the-art database.
So I always would recommend running privacyIDEA with Apache. This is describe in this post.
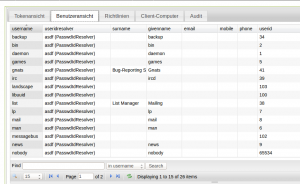
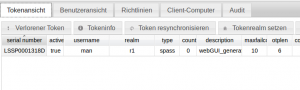
I was wondering what this paster and sqlite could do, So I created a realm containing the local users from /etc/passwd and assigned a simple pass token to one of these users.
Now I was able to issue an authentication request by calling the API like this:
https://myserver:5001/validate/check?user=man&pass=test
Now I used ApacheBench to call this URL:
% ab -n 1000 -c 10 -s 5 https://172.16.200.139:5001/validate/check?user=man\&pass=test This is ApacheBench, Version 2.3 <$Revision: 1528965 $> Copyright 1996 Adam Twiss, Zeus Technology Ltd, http://www.zeustech.net/ Licensed to The Apache Software Foundation, http://www.apache.org/ Benchmarking 172.16.200.139 (be patient) Completed 100 requests Completed 200 requests Completed 300 requests Completed 400 requests Completed 500 requests Completed 600 requests Completed 700 requests Completed 800 requests Completed 900 requests Completed 1000 requests Finished 1000 requests Server Software: PasteWSGIServer/0.5 Server Hostname: 172.16.200.139 Server Port: 5001 SSL/TLS Protocol: TLSv1.2,AES256-GCM-SHA384,2048,256 Document Path: /validate/check?user=man&pass=test Document Length: 135 bytes Concurrency Level: 10 Time taken for tests: 41.964 seconds Complete requests: 1000 Failed requests: 0 Total transferred: 373000 bytes HTML transferred: 135000 bytes Requests per second: 23.83 [#/sec] (mean) Time per request: 419.643 [ms] (mean) Time per request: 41.964 [ms] (mean, across all concurrent requests) Transfer rate: 8.68 [Kbytes/sec] received Connection Times (ms) min mean[+/-sd] median max Connect: 2 11 14.4 9 218 Processing: 121 407 270.7 332 3340 Waiting: 120 406 270.8 332 3340 Total: 126 418 272.0 342 3350 Percentage of the requests served within a certain time (ms) 50% 342 66% 401 75% 456 80% 499 90% 678 95% 948 98% 1318 99% 1632 100% 3350 (longest request)
This was done on a Virtual Machine running in VirtualBox with 2 processors and 2GB of RAM. The host machine is an Intel i7-4702MQ CPU @ 2.20GHz.
24 Authentications per seconds, no failed requests look rather good to me.
So why not give it a try?




3 thoughts on “How to install privacyIDEA OTP server on Ubuntu 14.04”
Followed your installation documentation for ubuntu 14.04. Connecting to server-ip:5001 just get internal server error.
An internal error is often caused by an incorrect file permission. In your case you should see more information on the terminal, where you ran the server. In case of running from within Apache, you can see it in apache error log.
But my bad! This howto is outdated. Please refer to the documentation at readthedocs.