Flexible and individual Workflows
Today we release privacyIDEA 3.2. Two new event handler modules allow for even more flexible workflows. Integrating with external logging tools like Logstash or Splunk are much easier now using the container audit module and the file audit module. Using Trusted JWTs makes it much more robust to integrate any existing portal with privacyIDEA.
Request and Response Event Handler
The event handlers have been around sind version 2.12. Every version somehow improved the event handler. They allow for a very flexible way to define actions and responses in privacyIDEA. Read a recent post about the script event handler or take a look at the complete list of event handlers.
With version 3.2 the administrator gets two new event handlers – the Request Mangler Handler and the Response Mangler Handler. You notice the word mangle – these handler allow to modify, delete or add any arbitrary REST request parameter or JSON response parameter, given the administrator unseen flexibility to flex the privacyIDEA system to the very specific need!
The Response Handler could be used to delete certain response information, after it is used e.g. by a notification handler. For example the notification handler could read this information to notify the user but then the Response handler would delete this information, so that a help desk user is maybe not able to read a randomly set password in a response. The resulting possibilities are unimaginable.
We are very excited to see how administrators will use these features!
Audit data everywhere
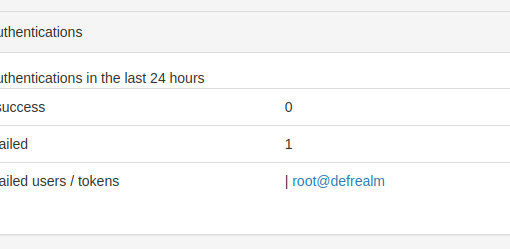
privacyIDEA runs in big environments. Because it integrates so well. privacyIDEA also creates an Audit log (and a log file – for debugging purposes). However, the log file is great, since every HTTP request has its dedicated audit entry.
It should be easier to add the audit data to these locations, where bigger organizations aggregate and keep their Log data. These are systems and services like Logstash or Splunk. As a first step privacyIDEA 3.2 comes with two new audit modules, the File Audit Module, that can write audit information to a plain text/log file and a Container Audit Module, that can combine any number of Audit Modules, so that privacyIDEA can write audit data to all of these modules.
We hope that this is a big leap forward to get your information to the right place!
The trusted JWTs
Did you ever want to have users manage their privacyIDEA tokens in an existing local portal? Or your helpdesk users get privacyIDEA information into the ticket system they are using? With privacyIDEA 3.2 it gets much easier now. The administrator can define trusted JWTs. I.e. he can define trusted public keys and which user this public key can impersonate.
The mentioned portal will simply use its private key to create JWTs, that are then trusted by privacyIDEA. No need to create service accounts, share passwords or other credentials.
The complete changelog
There are a lot of new enhancements, which administrators and helpdesk users will probably like for a daily use. A lot of enhancements, which we needed to provide better and easier service for certain installations.
Besides the event handlers also policies have been improved. The administrator can now use any arbitrary HTTP header in the policy condition. This way policies could be strictly bound to certain http_agents.
To improve the roll out process, the event handlers can match for the roll out state of a token. The notification handler, that was already able to send email or SMS, can now also write files to a spool directory. This way information can be easily passed to 3rd party systems or this data can be processed further like printing PIN letters.
We also did some improvement of the authentication process for the PUSH token so that it is not necessary to require a service account to verify the answered challenges.
The complete changelog can be found at github.
Go and get it
privacyIDEA 3.2 can be installed from source from github, via the Python Package Index or using ready made packages for Ubuntu 16.04 LTS and 18.04 LTS. The builds for Ubuntu are now based on Python 3.
Image by BarbaraALane on Pixabay.




Start the discussion at community.privacyidea.org