 We are happy to announce that we released privacyIDEA 2.8 with great improvements in U2F and SAML.
We are happy to announce that we released privacyIDEA 2.8 with great improvements in U2F and SAML.
Features
U2F authentication at other services
privacyIDEA was heavily improved as far as U2F is concerned. privacyIDEA can now take trusted facets, so that you can use the U2F token, that you registered with privacyIDEA to authenticate at other services on your network. Of course, due to the U2F protocol specification this is limited to other hosts in the same domain.
U2F for Single Sign On
The simpleSAMLphp plugin was enhanced to also support U2F. It is now possible to authenticate with the U2F token which you registered with privacyIDEA to a simpleSAMLphp Identity Provider (IdP). This way you can have Single Sign On at all services you wish to.
In addition the simpleSAMLphp plugin was enhanced so that you can use any challenge response token like SMS or Email or HOTP and TOTP in challenge response mode with you SAML login.
Web UI themes
It is now possible to change the style of the web UI without running into troubles when updating. Changes will not be overwritten.
Authenticate with REMOTE_USER
You can now use the webservers HTTP Basic Authentication to authenticate to the Web UI of privacyIDEA. This way you can use any Apache auth module (like shibboleth for SSO) to login to the privacyIDEA management interface.
Fuzzy Authentication
We started ideas with fuzzy authentication. In this release we added simple limits for successful and failed authentications: auth_max_success, auth_max_fail and last_auth.
It allows you to limit successful or failed authentications for a given time window. E.g. this way you can assure that a user does not perform more than 3 failed authentications within 5 minutes. This is one way to limit the risk for brute force attacks.
last_auth lets you define, what should be the last time a user has to have authenticated. If you set this to 2 month and the last authentication of the user is over for more than two month, the user will not be able to authenticate – even if he provides the right credentials. This is to avoid “sleeping” accounts. In big setups it might be difficult to control which user is still there and which user is gone. This can happen at large setups like universities. If there is an inactive user who did not login within the last year, the student is probably not at the university anymore. So he should not login at all.
Enhancements
- Allow mangle policy when fetching ssh keys
- Add realm support to ownCloud plugin
- Support Drupal passwords in SQL resolver
- Add validity period to token enrollment
- Set default enrollment token type in Web UI
- Add scope to LDAP resolver
Fixes
- Fix failcounter reset for challenge response tokens
- Fix confusing DB errors (column exist) during installation
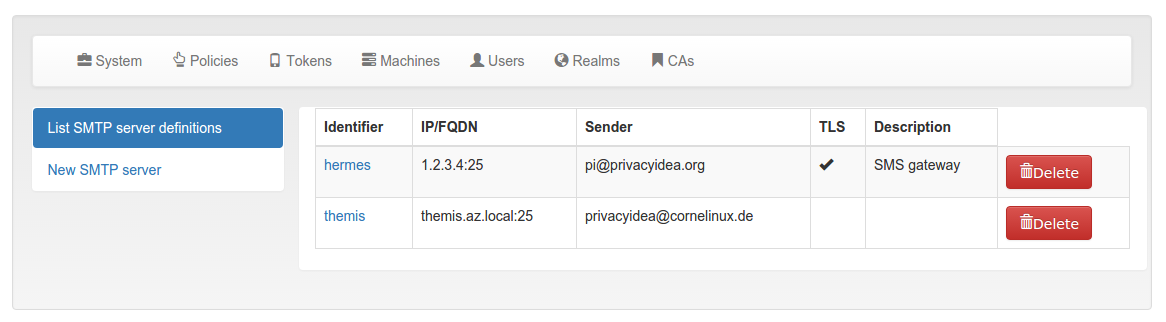
- Fix email token TLS checkbox saving
- Fix TOTP testing in Web UI
- Fix SMS config loading in Web UI
You can install and upgrade privacyIDEA in the usual ways.
We are looking forward to your feedback.



One thought on “privacyIDEA 2.8 with SAML and U2F”